
It’s the middle of 2021, and the recruitment industry continues to evolve around us. To successfully navigate all these changes, it is helpful to educate yourself on the unique opportunities and threats facing today’s recruitment industry.
In this article, we will tackle some of the most common threats and opportunities in recruiting industry that arise nowadays:
- Loads of candidates.
- Making use of the candidate pool.
- Poor time management.
- Effective Communication.
- Constant evolution.
- Recruiter/Manager Disconnect.
- Employer Branding.
- Technology Evolution.
Let’s get straight to the point!
Loads of Candidates

This sounds like the opposite of a problem, and in some ways, it is. More talent increases your odds of finding well-matched candidates rather than simply finding the best that’s available.
It does become a problem when there are so many candidates to source and to receive resumes from that it increases your administrative load. If your time management isn’t sharp, you could find yourself overwhelmed and essentially wasting the benefit of so many candidates.
Recruiters need to be able to find, select, secure, and onboard candidates. If you are overwhelmed, you are likely to do a poor job of some or all of these steps. Making a less-than-satisfactory hire or failing to situate the hire in their new job properly could lead to higher turnover and even more work for you and less profit for everyone.
It sounds like a nightmare!
Making Use of the Candidate Pool

You can find some fantastic candidates out there if you give yourself the time to invest in the search. However, no matter how good a candidate is waiting out there, you might not find or land them if you don’t have a targeted approach.
Try these tips to make the most of this opportunity:
- Create ads that not only inform candidates of the job but speak to them in an engaging and target-candidate-appropriate way. You can check some of the creative recruitment strategies we have here.
- Look for cultural compatibility and a mix of both hard and soft skill sets.
- Communicate intelligently with the candidates to reflect the investment the company wants to make in their employees.
Poor Time Management
Sorting through all these candidates takes time, and you don’t want to rush through it.
Tailor your ads to your target audience
The point mentioned in the previous section about creating engaging and candidate-appropriate ads may be the most crucial recruiting task for improving efficiency.
When you target your employer branding and ads to attract suitable candidates, you:
- Eliminate nearly all the need for sourcing.
- Create a situation where candidates self-screen themselves.
- Have won most of the battle of wooing the candidate.
So, by investing a little time initially in perfecting your targeted ad approach, you save a lot of time, headache, and room for error in the rest of the hire.
Communicate effectively
It is also essential to communicate effectively with candidates. To save time, many recruiters do sloppy things like sending the same candidate a generic email repeatedly. This results in a waste of the recruiter’s time, angry candidates, and the attraction of only desperate candidates.
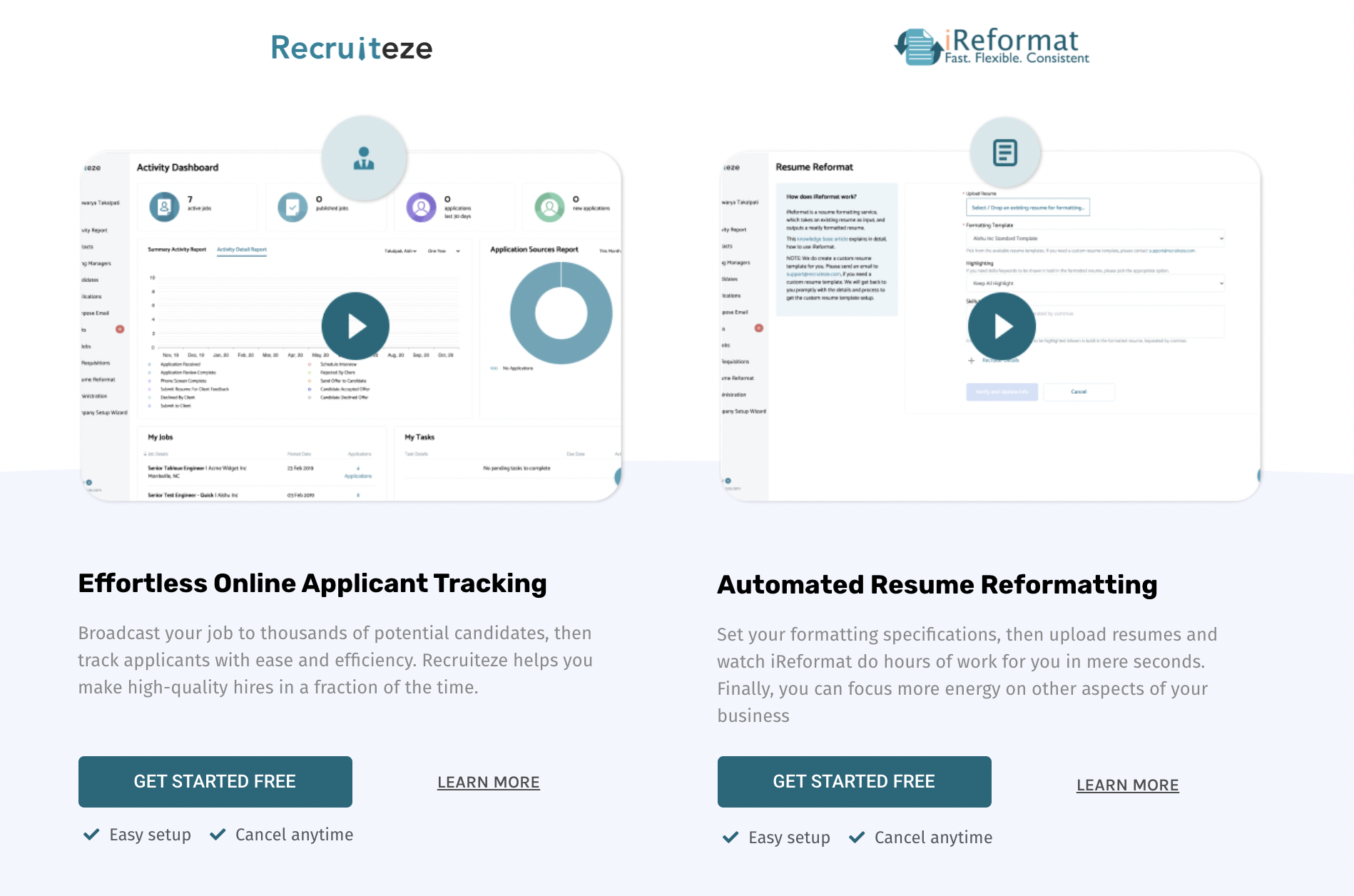
You do want to automate as many processes as you can. ATS such as Recruiteze are excellent for this. Communication is a wonderful area for automation, but only if done wisely and sparingly.
Some businesses have utilized creative and efficient techniques like digital interviews, self-screening, and open-houses to attract interested candidates and weed out less-committed ones. You might want to do the same.
We have described the open-house concept in our post on creative recruitment strategies:
Self-selection screening is a way of pre-qualifying applicants. Simply introduce an open invitation event to candidates before the interview stage. Those who turn up are keen – those who don’t, not so much. This also allows you to assess candidates in a group environment while giving candidates more insight into who you are and what you do.
Recruiter/Manager Disconnect
This is not a new problem; instead, the tragic thing is that this is an ancient problem that has never been appropriately addressed. As a result, recruiters and hiring managers don’t understand each other and are not on the same page. This means recruiters are working hard to find a square peg to fit in a round hole.
According to a study from iCIMS in 2014, the figures are pretty frightening.
“80% of recruiters think they have a ‘high’ to ‘very high understanding of the jobs for which they recruit”, while “61% of hiring managers say that recruiters have, at best, a ‘low’ to ‘moderate’ understanding of the jobs for which they recruit.”
This is a gap that cannot go unaddressed.
A Bersin study in the second half of 2016 confirmed that the need to improve recruiter and hire management relationships was still paramount.
Fast forward to 2021, and people are still discussing this problem.
Few companies have nurtured the recruiter and hiring manager relationship, so if the relationship does improve, all parties enjoy more direct success and less headache and gain a competitive advantage over their peers.

Some of the things you can do to address this are:
- First, understand the importance of communication. Make sure that you have effective communication and address everyone’s concerns. Communicate with them regularly to keep up with hiring news and company goals that may impact hiring decisions.
- Understand the corporate culture. Recruiters and managers share different objectives and views, but it is essential to be aligned with the company’s culture in your ideas.
- Understand the company’s goals. Finally, managers need to ensure that recruiters understand the overarching company’s goals.
- Ensure that recruiters understand their roles and goals. Sometimes it is easy to get off track, and managers should make sure to check up on their underlinings to see if they are still on the right way with their recruiting strategies.
- Manage expectations. Set up a time to discuss the hiring manager’s expectations and create a joint plan to meet hiring goals.
- You might also read this post on how to engage the hiring manager/client in a solid relationship.
Employer Branding
Employer branding, or the act of branding yourself to employees as carefully as you do to customers, is huge right now. If you’re utilizing it, it’s an opportunity; if not, it’s a threat, and your competition is going to get way ahead of you.
How to Use Employer Branding to Better a Business in Every Way
In the process of developing an employer brand, the business owner will discover so many opportunities to increase employee engagement and better their advertising techniques. In turn, these steps will also save on hiring costs and increase productivity. It’s hard to argue with those kinds of benefits.
First, they want to evaluate their current company culture for opportunities to engage better and reward employees. They might talk to them about the things they like and don’t like about the job, things that are troubling them in their home life, and things they’d like to see happen in their future. These points will give valuable insight into how to inspire and motivate employees.
Once they’ve started acting on the things they’ve learned with plans like recognition programs, better vacation plans, more flexible hours, or equipment updates, they can advertise these changes, and therefore cool new perks to potential new candidates.
Recruiters can make sure to both advertise these perks and treat candidates during communications in such a way to reflect the company culture of the client.
These are some of the major factors weighing on recruiters and their clients right now. However, as you can see, the threats and opportunities often switch places depending on how a situation is handled. By utilizing the tips in this post, particularly the point about optimizing your business to manage change, you can be prepared for any opportunity or threat that comes up.
Constant Evolution
Technology, business, and the workforce are constantly changing, sometimes overturning norms seemingly overnight. For example, for decades, it may have been advantageous to recruit in one manner, but now it is wrong.
Today, recruiting is taking place mainly on social media and the digital sphere overall. It is focused far more on culture than financial reward and may involve short-term employees more than long-term employees.
Some of these aspects are completely new, such as social media. Others challenge the way recruiters have been trained to think. Without adapting, recruiters can be held back, and in this candidate-driven and highly competitive time, recruiters could struggle with losing top talent to other companies.
Tips for Keeping Up with Fast Changes

Incorporate social media and mobile devices in your recruiting efforts, and be on the lookout for advancement. If a new platform becomes popular with your target candidates, start planning to move into that space.
Talk to your candidates and listen to what they say. Ask yourself questions like:
- What do they need or wish was different?
- What are their hopes for the future?
- How are they searching for their ideal job?
- Who are they admiring?
If you notice several people giving the same answers, listen now. You might be about to catch the wave of the next new trend.
Most importantly, make your business adaptable. This is excellent advice regardless of what the changes will be. You want a goal-oriented approach to your business with measurable results so you can quickly notice when something is going amiss.
Also, prepare for the future. Don’t just evaluate your current challenges. Instead, try to anticipate challenges that may occur in the future.
Technology Evolution
Even the birds on a tree know this by now, but recruiting has changed tremendously in the last two decades.
Keeping up and adapting to new emerging technologies is crucial to remain on top of your game.
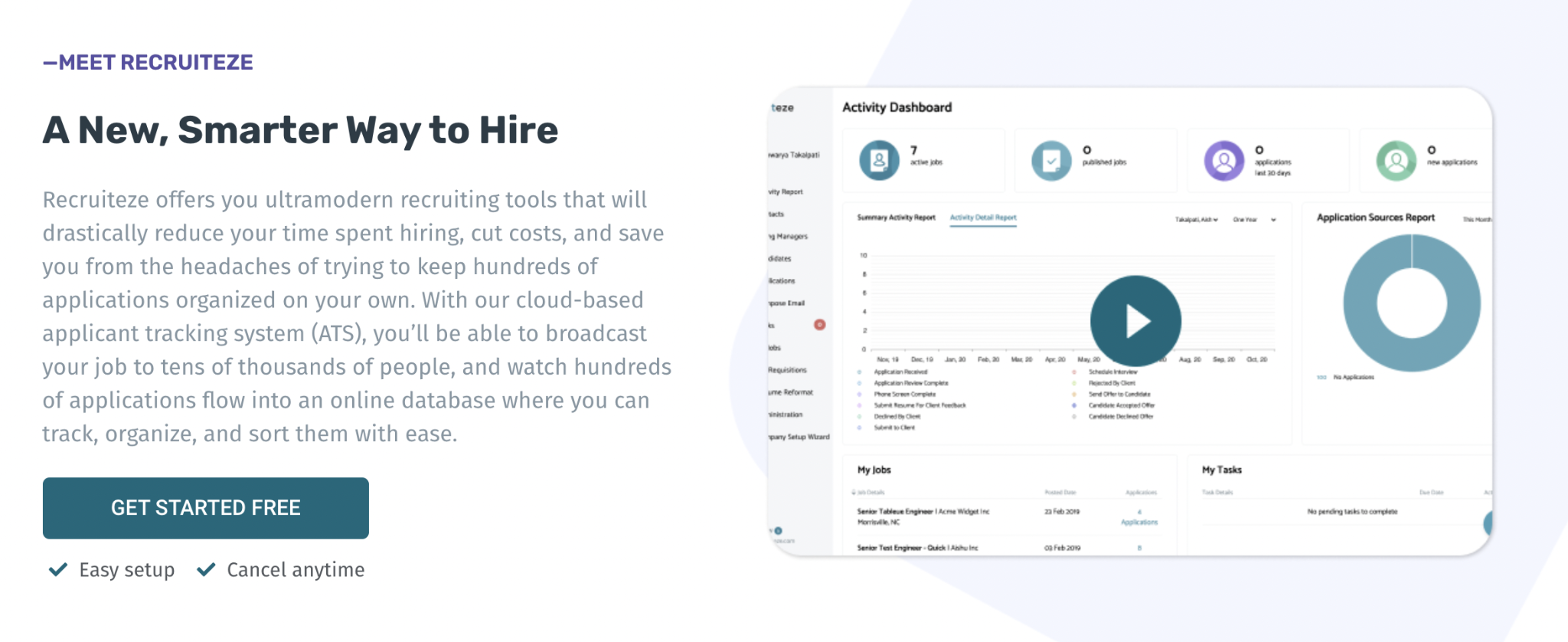
Searching for sound recruiting systems can be challenging and tiresome, but finding the right one can be even worse. However, this might just be your lucky day since you have stumbled upon Recruiteze!
Recruiteze is a modern recruiting solution designed for small to mid-sized businesses.
With it, you’ll get a responsively designed system that comes complete with a custom job board, unlimited email templates, unlimited automated resume formatting and parsing, and so much more.
There is no obligation, and using our fantastic software makes hiring easier.
You can try it for free for 30 days today!
Featured articles from our blog:
